JS Business Solutions Blog
Projects are a big part of doing business. When we mention projects it’s typically in reference to IT projects, but for your average business, when they think of projects it means specific jobs coordinated for specific clients. In this environment it is essential to get the people on a project team on the same page and working towards a shared end. In this week's blog, we thought we’d discuss the importance of solid project management and how certain technologies can help project managers improve their turnaround times.
There are a huge number of apps available on the various app stores—3.5 million and 1.6 million on the Google Play store and Apple’s App Store, respectively—and, while most of them are sufficiently secure to use, many of them aren’t. It can be hard to tell the difference between the two at times, so it is important that you and your team are protecting your business however you can. Let’s discuss the topic of security, as it pertains to mobile app stores, and why the issues have transcended security.
Cybersecurity has gradually become more and more of a focus for modern businesses as threats to their data and general operations have mounted over time. This means that businesses need to approach their security with a multifaceted strategy, involving a combination of the right tools and IT support and the training to use them. Let’s take a few moments to dive into security training and why it is so critical.
Most businesses leverage the cloud in at least some capacity, whether cloud-based apps or cloud-based infrastructure. In any case, using the cloud comes with inherent security questions that must be addressed during the planning, implementation, and launch phases of any solution. Let’s go over some of the ways you might protect data and applications stored in the cloud.
Zero-day vulnerabilities are never fun, but this is especially the case with popular devices, like the many that use the Samsung Exynos modem. Google’s Project Zero has discovered 18 such vulnerabilities in these chips, four of which allow for remote code execution. Why should you be concerned about these vulnerabilities and what can you do to minimize your risk?
Technology has done some incredible things, especially in the past couple of decades, so it’s wild to imagine that someday, innovative new tools like ChatGPT will no longer be as cutting-edge as they might seem today. The reason is simple: most technologies today were once world-shattering and innovative, but with time they have become normalized.
Oh, the afternoon meeting, the woe of many office workers around the world. Sometimes they are fine, but other times, it’s very clear that they are not always an effective use of your time. Despite this, there is still a heavy emphasis on meetings in the workplace, to the point where some employees feel that their time is being wasted and misused as a result—a premise that is supported by surveys and research.
Wearable technology is all over the place in your office, whether you realize it or not. Consider how many of your employees wear smartwatches or health trackers. All of these devices tend to enrich the lives of those who use them, but they can quickly become network security risks if you aren’t prepared to handle them on your company network. Let’s go over what you need to consider to protect your business from wearable technology.
Technology has become a fundamental need for businesses of all sizes, with even small businesses needing to seek out options to cover their shifting needs. Fortunately, this technology has also become more reliable and readily available…and as a result, small businesses have more opportunities than ever to give their operations a welcome boost.
Uh oh. You were trying to be more secure and decided to set up multi-factor authentication. However, you’ve just discovered how important the other factors are when it comes to authenticating your identity. Yes, you’ve found yourself unable to access your means of authenticating yourself.
So…what do you do now?
If we asked you to identify the one hour of your day when you get the most done, would you be able to tell us? Even more interestingly, do you know how to get the most out of your so-called “power hour?” Let’s take a look at some of the theories about how you can make the most out of your most productive time in the workplace.
One of the nice things about the Windows operating system is how many bells and whistles there are to benefit the user. Take, for example, Storage Sense, which is intended to help you deal with some file storage issues that are only too common both at the office and at home. Let’s take a closer look at Storage Sense and how knowing about its capabilities can be so helpful.
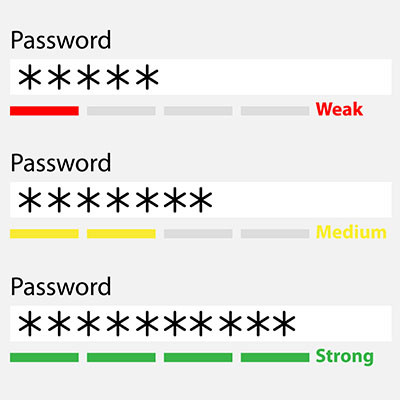
Cybersecurity has never been more important. There are millions of scams sent out every day that are ultimately targeting you and your employees’ password-secured accounts. Today, we are going to give you some tips on how to create passwords that work best to protect your data and information systems.
Make no mistake, you want your business to grow. There is no better sign that you are resonating with customers and providing the value you set out to deliver. Unfortunately, for a lot of companies, they simply aren’t prepared when their product or service takes off and it ends up ruining what could be a very good thing. Today, we’ll take a look at three actions you can take to keep your business humming along when it sees extraordinary growth.
Phishing is a word that has a couple of different meanings, depending on the spelling and context. Fishing, like the act of sitting down with a pole and trying to catch a fish, can be a relaxing, leisurely activity. Phishing, with a “ph,” is anything but that, and it can be a tiring and scary situation to navigate—particularly if you or one of your employees have fallen victim to an attack.
The sales process is an integral part of every business. How to get your products and services in front of prospective customers is the big mystery that every business has to solve. Technology can really help improve your business’ sales process. Today, we will look at a couple of technologies that work wonders to help your sales team be more effective.
Most people use their smartphones more than any other computing tool, and businesses must adapt to these trends if they want their employees to be as productive as possible. Businesses can capitalize on their employees’ smartphone use if they are strategic in their implementation of mobile device tools and strategies—including work profiles on Android devices.